How to Prevent PII Leaks When Your Team Uses AI Chatbots
New research shows 22% of files uploaded to AI tools contain sensitive data. Learn how to protect your organization from the growing threat of AI-enabled data leaks.
Expert articles on AI data leakage prevention, enterprise AI security, and compliance. Actionable strategies from security professionals to protect your organization.

New research shows 22% of files uploaded to AI tools contain sensitive data. Learn how to protect your organization from the growing threat of AI-enabled data leaks.

From HIPAA modernization to SEC AI disclosure requirements, navigate the new regulatory landscape with this comprehensive compliance guide.

A developer just leaked AWS keys to Copilot. The keys vanished before they hit the cloud. Here's why. See how Alex and Jordan protect everyone silently.

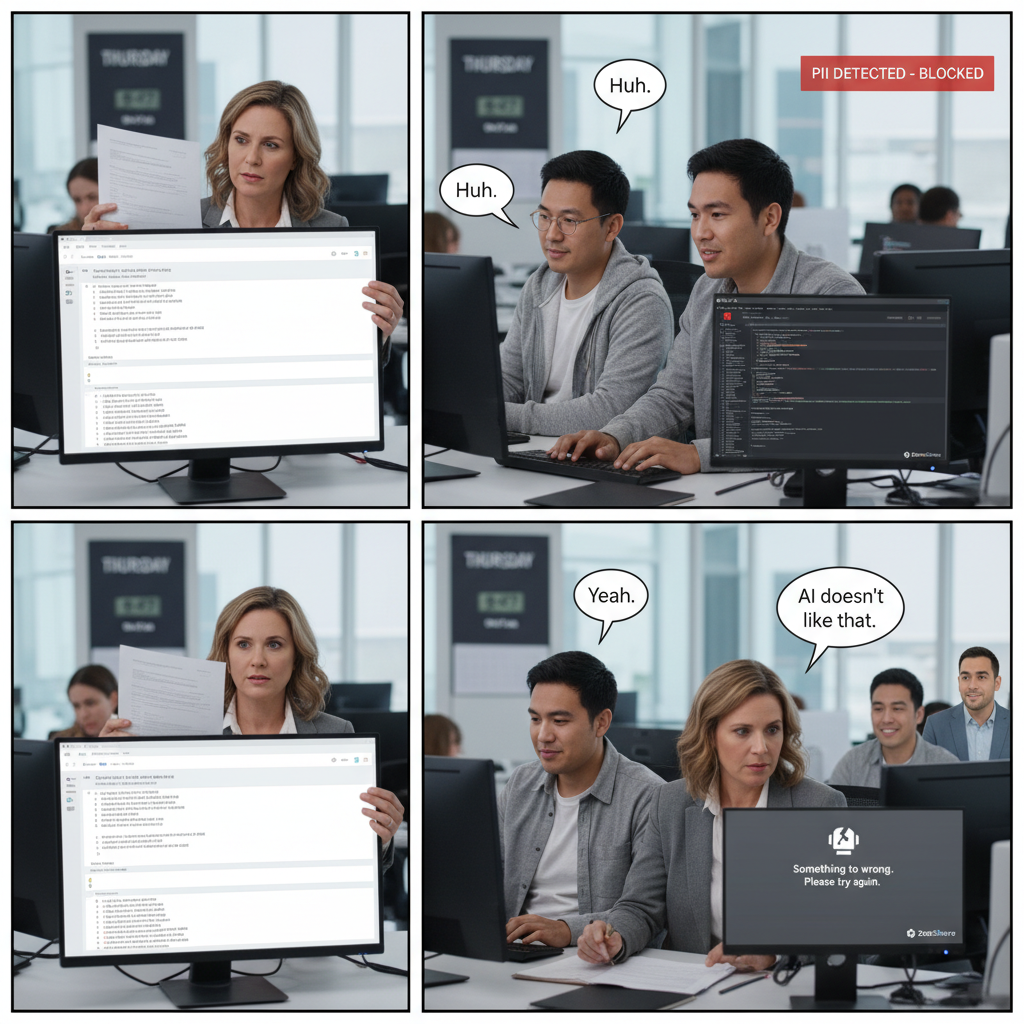
Support rep thinks she's great at prompting. She has no idea her PII is being stripped. Watch. See how Alex and Jordan protect everyone silently.

Traditional perimeter security fails for AI. Learn how to apply zero trust principles to protect your organization while enabling AI productivity.

Researchers extracted 2,702 real credentials from GitHub Copilot. Your developers are at risk. Here's how to protect your secrets.

With 20% of breaches now involving shadow AI, governance isn't optional. Learn how to build a framework that enables innovation while managing risk.

With 72.6% of sensitive AI prompts going to ChatGPT alone, you need a security layer that works across all AI tools. Here's how AI gateways work.

98% of organizations have employees using unsanctioned AI tools. New research reveals shadow AI increases breach costs by $670,000 on average.

The 2026 HIPAA Security Rule modernization introduces prescriptive AI requirements. Here's what healthcare CISOs need to prepare for.

Not all AI DLP architectures are created equal. We compare proxy, endpoint, API, and hybrid approaches with real performance data.

AI coding assistants are transforming development workflows. Here's how to maintain security without killing productivity.

Most AI policies are either too vague or too restrictive. Download our battle-tested template based on real enterprise deployments.

From prompt injection to training data extraction, understand the unique security challenges of large language models.

We put ChatGPT Enterprise through rigorous security testing. Here's what we found—good and bad.

What do SOC 2 auditors actually look for when assessing AI controls? A former Big 4 auditor shares insights.

Practical patterns for adding AI security controls to your microservices without creating bottlenecks.

A comprehensive walkthrough of GitHub Copilot's security configurations and what they actually do.

Risk registers for AI look different than traditional IT risks. Here's how to build one that actually helps.

Prompt injection is the SQL injection of the AI era. Deep dive into attack vectors and defense strategies.

Translate AI security risks into business impact with this framework for executive communication.

The EDPS released new AI guidance in October 2025. Here's what changed and what you need to do.

Your AI gateway is now critical infrastructure. Here's how to architect it for 99.99% uptime.

Shift left on AI security with pre-commit hooks that catch sensitive data before it reaches your AI tools.

47 questions to ask before approving any AI vendor. Includes red flags and deal breakers.

As RAG architectures proliferate, vector databases become attractive targets. Here's how to secure them.

Need to brief your CEO on AI risks? Here's everything they need to know in a digestible format.

With fines up to 6% of global revenue, EU AI Act compliance isn't optional. Here's your month-by-month roadmap.

Helm charts, resource limits, and scaling strategies for production AI gateway deployments.

Infrastructure as code templates for deploying AI security controls across AWS, Azure, and GCP.

Your employee just pasted customer SSNs into ChatGPT. Here's your incident response playbook.

Rate limiting, key rotation, and monitoring strategies for secure OpenAI API consumption.

AI-generated phishing emails are defeating traditional filters. Here's what security teams need to know.

A comprehensive overview of AI regulatory requirements for banks, investment firms, and fintechs.

How to build AI security controls that scale across thousands of tenants without breaking the bank.

Cursor is gaining popularity fast. Here's how to configure it securely for your development team.

Your vendors are using AI too. Here's how to assess and manage the downstream risks.

We tested Claude's enterprise security controls against our standard assessment framework.

How to test your AI defenses before the attackers do. Includes exercise scenarios and scoring rubrics.

US states are increasingly regulating AI. Here's a state-by-state breakdown of what applies to you.

On-device AI models present unique security challenges. Here's how to address them.

A deep dive into securing Amazon Bedrock deployments with proper AWS configurations.

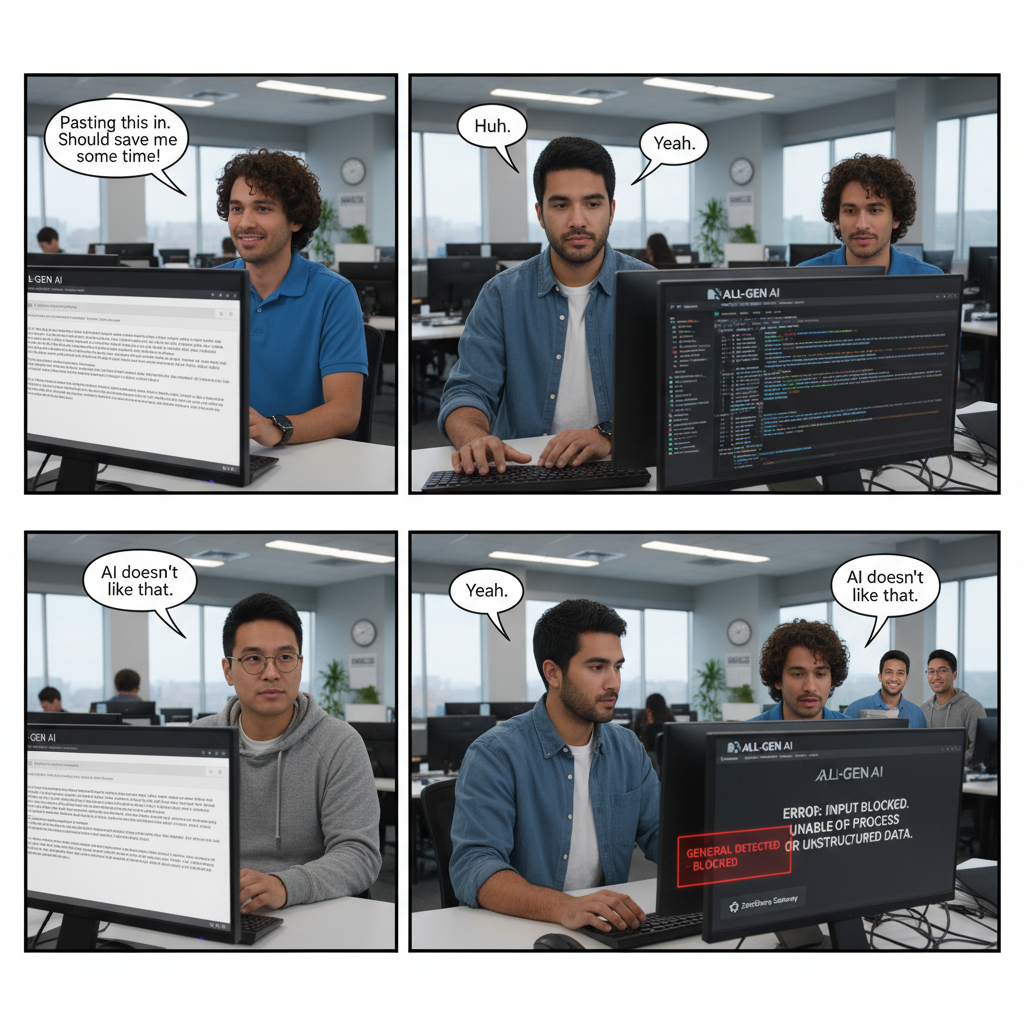
He closed a $2M deal and pasted the whole contract into ChatGPT. This is what the engineers saw. See how Alex and Jordan protect everyone silently.

Marketing pasted 23 customer emails into AI for a campaign. Zero left the building. Here's the trick. See how Alex and Jordan protect everyone silently.
The CEO announced 'AI-first.' Two engineers in the back didn't clap. They were already 3 years ahead. See how Alex and Jordan protect everyone silently.

50+ PII patterns. One invisible system. Nobody at this company knows it's running. Except two people. See how Alex and Jordan protect everyone silently.
I found 47 blocked API keys in one day. The developers thought Copilot was 'being picky.' See how Alex and Jordan protect everyone silently.

They deployed AI security with zero code changes. Users didn't notice. That was the point. See how Alex and Jordan protect everyone silently.
The CISO presented her AI security concerns. She didn't know they were already solved. Watch her face. See how Alex and Jordan protect everyone silently.
$4.45M. That's the average breach cost. This company pays $499/month instead. Here's their secret. See how Alex and Jordan protect everyone silently.

CFO: 'What's the ROI?' Engineer: '$499 vs $4.45M.' CFO: 'That's not ROI, that's survival.' See how Alex and Jordan protect everyone silently.

98% of companies have shadow AI. This one does too. The difference? Two engineers who don't sleep. See how Alex and Jordan protect everyone silently.
GDPR fine: €15M. HIPAA fine: $1.5M. Cost to prevent: $499/mo. Why do companies still gamble? See how Alex and Jordan protect everyone silently.

Episode 15. Something changed. The engineers finally spoke. What they said shocked everyone. See how Alex and Jordan protect everyone silently.

10 minutes. That's how long it took to deploy. Users noticed nothing. Attackers noticed everything. See how Alex and Jordan protect everyone silently.
14 days free. All features. No credit card. What's the catch? There isn't one. Here's proof. See how Alex and Jordan protect everyone silently.
We use cookies to analyze site traffic and improve your experience. Learn more in our Privacy Policy.